So your threat model assumes an actor with a quantum computer capable of breaking RSA, but not a regular computer capable of filtering by IP address?
See also https://lemmy.world/u/p1mrx
- 1 Post
- 46 Comments
USB 2.0 vs. 3.0 data has nothing to do with USB PD charging wattage.

 72·1 year ago
72·1 year agoWait till you hear about the origins of Volkswagen.

 3·1 year ago
3·1 year agoThat’s 4200 TWh/year, or 480 GW.
Though that ignores the power consumption that isn’t electrical yet, like transportation and heating.

 31·1 year ago
31·1 year agoCurrently that backup/storage is mostly fossil fuels, so building nuclear would displace fossil fuels. As long as nuclear remains expensive, we will only build it because not emitting CO2 is socially valuable.
Nuclear would have to get a lot cheaper to eat wind/solar’s lunch. Maybe that could happen someday, but it’s not worth worrying about now.

 158·1 year ago
158·1 year agoThis is only good news if it displaces thermal coal and gas generating stations.
Is there another plausible scenario? Wind and solar are getting so cheap, that displacing either with nuclear is like flushing money down the toilet.

 1·1 year ago
1·1 year agoA sufficiently-large pile of cash could redirect that tritium from weapons to fusion development when the time comes. Seems better than not having enough supply anywhere.

 224·1 year ago
224·1 year agoIt’s interesting that India is building lots of heavy water reactors, because they produce tritium, which would be useful for bootstrapping fusion: https://www.science.org/content/article/fusion-power-may-run-fuel-even-gets-started

 4·1 year ago
4·1 year agoOn Chrome, I only ever recall seeing the dialog when I install an extension, or if an extension is updated to use additional permissions.
Firefox MV3 is different, in that the all_urls permission cannot be granted on install. If an extension requests all_urls, it installs with the permission disabled. The user has to manually enable it for one site or all.
IPvFoo is mostly useless without all_urls, which is why I made it show that button until the permission is granted.

 5·1 year ago
5·1 year agoFirefox requires explicit user interaction to grant the
all_urlspermission, although this only applies to Manifest V3. Here’s what it looks like on my extension:
I could’ve just reverted to Manifest V2 to avoid that step, but V3 will probably become mandatory someday.
At Fukushima, Zirconium-DHMO reactions produced an explosive gas that blew up 3 buildings!

 1·1 year ago
1·1 year agoMethane is certainly less bad than coal, but it still moves carbon from the ground to the air that we don’t know how to move back.

 1·1 year ago
1·1 year agoA lot of it’s going to Europe as a replacement for Russian gas.
The main problem is that everybody’s been switching from coal to gas instead of wind/solar/nuclear, as if drinking more water makes it ok to piss in the pool.

 17·1 year ago
17·1 year agoWhen I was in ~9th grade ordering 72-pin SIMMs, I read MUST BE INSTALLED IN PAIRS and assumed that vendor only shipped to France.

 6·1 year ago
6·1 year agoIn this case, disabling IPv6 is actually the right move. If the VPN provider doesn’t support IPv6, then there’s no way to allow to allow IPv6 Internet traffic without causing a leak/VPN bypass.
The right move for the VPN provider is to support IPv6. The right move for the user is to take their business to a provider that does.

 31·1 year ago
31·1 year agoThough I still wouldn’t want to live there; the area has been evacuated for good reason.

 7·1 year ago
7·1 year agoRadiation levels have decreased since the accident in 2011:
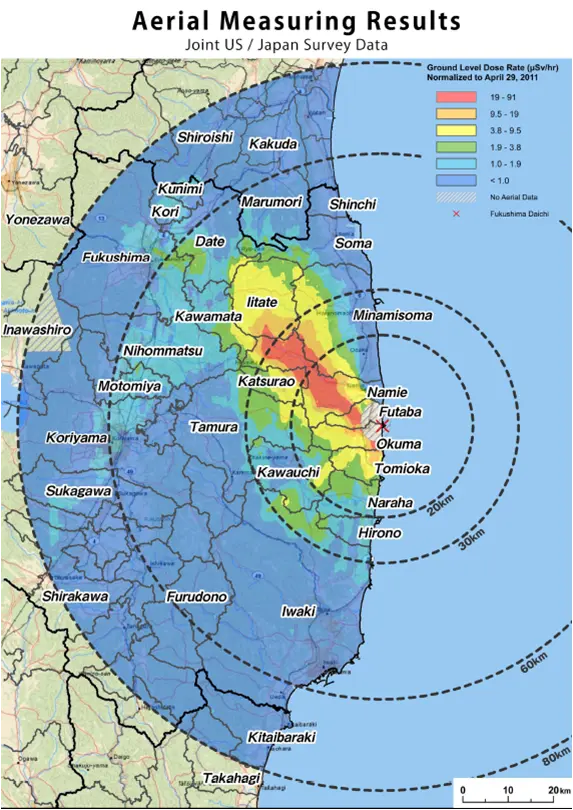
https://upload.wikimedia.org/wikipedia/commons/0/06/Fukushima_radiation_dose_map_2011-04-29.pngNote that on Safecast, you can enable “Crosshair” in the hamburger menu to see the actual numbers.
The central blob area is currently around 5 μSv/hr, so if you live there for a year it’s 44000 μSv, or 44 mSv. The xkcd chart says 100 mSv is the lowest one-year dose clearly linked to increased cancer risk.

 8·1 year ago
8·1 year ago“Those who cannot learn from history are doomed to repeat it.”
There probably is some value in understanding why “evil” things were attractive to people at the time, because if you believe that evil always looks unambiguously evil, then you might fail to notice when it happens again.


A VPN encrypts traffic between your device and the VPN server, and any packet on that path includes your IP address. So anyone attempting to decrypt your VPN traffic can trivially distinguish your packets from other users of the VPN server.